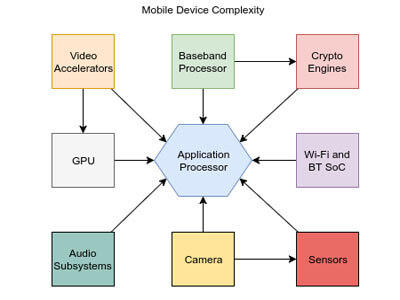
Mobile Device Block Diagram
As you can see in the above image, Application Processor (AP) is at core of the system of any modern mobile platform. As it is getting most of the attention from security researchers, attackers has been gradually shifting their attention to other less-attended parts such as sensors, camera or Wi-Fi & BT System on a Chip (SoC).
Today we going to focus on Wi-Fi System on a Chip (SoC) itself and how it has affected millions of smartphones and smart gadgets, including Apple iOS and many Android handsets from various manufacturers. Broadcom’s Wi-Fi SoC is the most used Wi-Fi Chipset today. The list of devices includes all iPhones since iPhone 4, Google’s Nexus 5, 6 and 6P and Samsung’s flagship Android smartphones.
Google Project Zero researcher Gal Beniamini has discovered several severe security flaws including remote code execution, privilege escalation and information disclosure vulnerabilities in Broadcom Wi-Fi SOC.
He has published a detailed two-part blog post on this issue. One explaining the Broadcom Wi-Fi chipset architecture and its vulnerabilities. Second part describing how to exploit those security flaws.

Image: Sarah Tew/CNET
The vulnerability was described as the stack buffer overflow issue. According to the researcher, this stack buffer overflow issue found in Broadcom firmware could lead to remote code execution vulnerability, allowing an attacker in the smartphone’s Wi-Fi range to send and execute code on the device.
An attacker who is in Wi-Fi range can exploit the security holes to take complete control of a vulnerable device without any user interaction. As a result he/she will be able to anything. Such as installing malicious apps, like banking Trojans, ransomware, and adware to name a few.
Fortunately all the responsible vendors have released necessary patch to fix this issue.
Apple released an emergency update this week for iOS to address the remote code execution vulnerability.
The Broadcom flaws were also patched in Android with the release of the April security updates.
Samsung has also released maintenance updates this week for its Android devices.
If you are using one of the mentioned phone from above and yet to install the updates.
Do it now.
Thanks for reading this article.
Have a good day.