
securityintelligence.com
New Trojan named CamuBot especially targeting commercial Bank users has been used to steal money from business customers in Brazil.
IBM x-force engineers who first tracked it down and reported it, identified the new Trojan highly sophisticated and very much different in how it operates comparing it previous financial Trojans like TrickBot, Dridex or QakBot. Camubot first appeared in Brazil in early august of 2018.
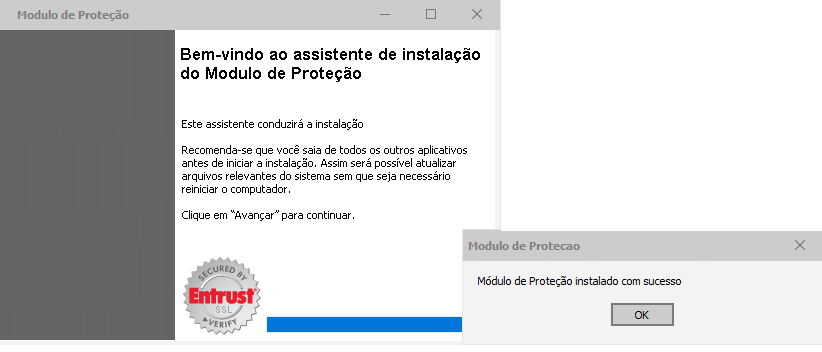
Unlike other banking Trojans, it does not attempt to hide it installation process. Camubot fools the end user using legitimate bank logo, when in reality a Trojan application is getting installed in disguise.
How does it happen?
Camubot uses good old Social Engineering tactics to find business that uses a certain bank for financial transactions. Then its operator’s places a phone to a user to mostly like use the particular bank to find out bank account credentials. Identified them as bank employees they instruct the user to browse to a infected URL to find out whether his/her security postures in up to date. Of course as the result comes back as negative, attackers convinces the user to install a new security software to improve the scenario.
securityintelligence.com
As it gets downloaded and installed with admin privilege, on the background Camuget gets executed on the user device. Furthermore, it also create an exception for the program on windows firewall along with a SSH based proxy connection.
After that, user gets asked to visit a phishing website when necessary bank account login credentials are needed to entered. As users does this, attackers get hold of that information to conduct fraudulent activities.
It also has the capability to bypass two factor authentication such as OTP, 2FA or fingerprint which are usually used by Banks to secure a user account.
Even though it hasn’t been spread outside of Brazil as of now, researchers assume to may do so in the future.
Thank you reading it.